Bankbot has become a very popular Android botnet since it’s source code was leaked in an underground forum. Since it’s code was free for users to modify, different variations have been seen from its original one.
Typically, Bankbot hardcodes the applications it wants to target and the urls it will contact. This can be appreciated checking a regular .dex file. On the other hand, modified versions of Bankbot grab the targets from a remote server thus nothing can be found without Dynamic analysis.
But there’s also this one that has been spotted in the wild but not much has been heard, and it stores the information and some functionality in a .so file separated from the original .dex file.
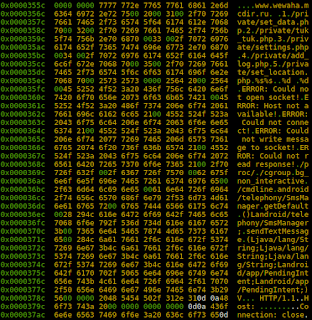
It contains an ARM64 SO file named libnative-lib.so. What information can we get from here? Taking a quick glance at the file’s hex content we can see interesting strings from the start:
We can figure out it connects to a wehaha.mcdir[.]ru domain and has different strings related to HTTP posts, so let’s try to grasp the functionality.
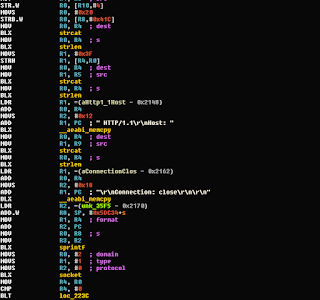
We can appreciate a HTTP POST function with some hardcoded stuff, which will be used by the trojan to send remote information to the different c&c endpoints.
It will try to run gethostbyname() and check whether it’s able to connect with the remote domain or not.
It also contains a function called getProc(void) which tries to fetch information from /proc, for example /proc/cmdline trying to check information like the current status of the kernel (R-O)
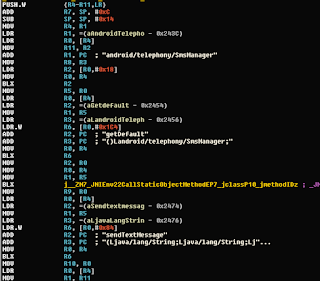
And last but not least important we count with a function called send_sms. This function grabs the default /android/telephony/SmsManager/ and sends an SMS with the specified content through the sendTextMessage method.
And this is all of it for now, there’s more functionality in the library but it’s mostly custom methods for string manipulations such as splitting, replacement, checking indexes…
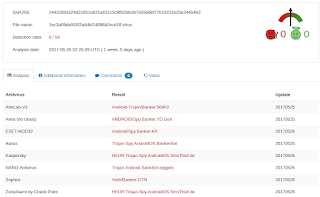
Also, it’s worth mentioning that the sample has less detections than a regular bankbot sample with 8 out of 54 detections




No comments:
Post a Comment